Integrated security workflow automation tools can save security teams days, if not weeks, of work. When used effectively, these tools can streamline processes and operations, enable quicker response times, and reduce the rate of human error.
This guide describes essential best practices to help maximize the value of security workflow automation tools through effective implementation.
Security workflow automation best practices
Why use automated security workflows?
Security teams spend an average of three hours a day manually triaging around 4,484 alerts. In 2023 alone, 26,447 vulnerabilities were disclosed, a massive increase from the 8,051 disclosures the previous year. It’s no wonder security teams are overwhelmed, suffering from alert fatigue and burnout.
However, there are ways to lessen the burden. The key is to create efficiencies by reducing manual, repetitive tasks; this can be achieved by leveraging security workflow automation.
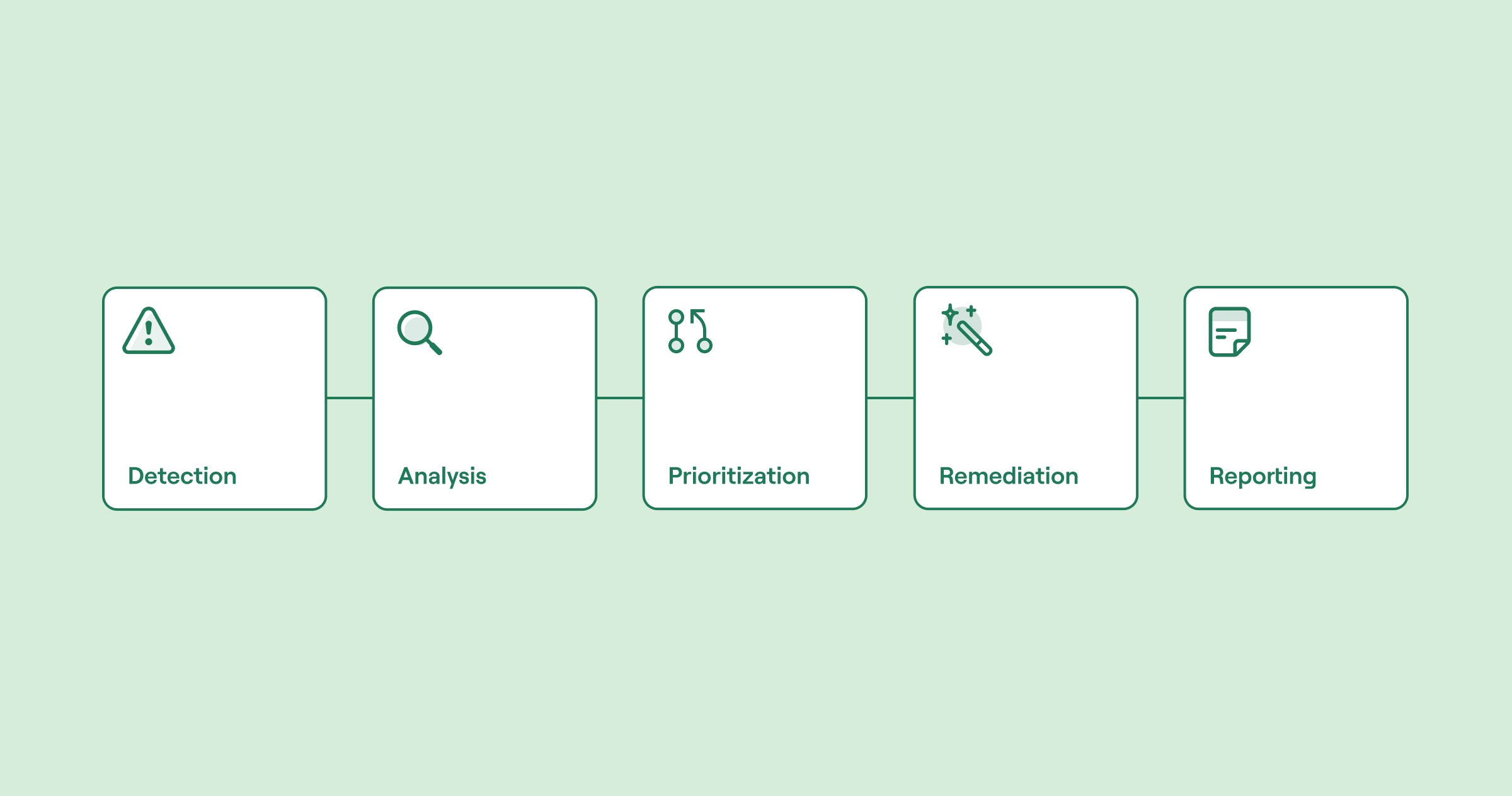
Threat detection automated workflow - detection, analysis, prioritisation, remediation and reporting (source)
Workflow automation tools orchestrate and route tasks or information among people, devices, and services based on predefined rules and triggers. They streamline processes and operations, offering increased efficiency, and can reduce the risk of human error.
Traditional security automation approaches and challenges
Security automation has existed for years, but historically, it was challenging to implement, existing in low-level scripting and rule-based systems. Security analysts would manually write scripts to automate everyday security tasks, like an analyst writing a script to parse log files for indicators of compromise (IoCs). This manual approach is incredibly complex and time-consuming.
The emergence of security incident and event management (SIEM) platforms led to easier log collection and centralization and the development of more sophisticated rule engines. However, SIEMs weren’t the answer to every problem: Analysts still contended with slow, human-reliant security processes, overwhelming alert fatigue, and growing numbers of false positives.
It wasn’t until 2015 that security orchestration, automation, and response (SOAR)—a term first coined by Gartner—emerged as a modern solution to the problem. SOAR tools enable analysts and engineers to build repeatable workflows across multiple tools and services. They are great at reducing the manual burden plaguing security teams. However, these solutions are often incredibly complex to configure, use, and maintain, thanks to their reliance on a team’s availability of coding knowledge. Low-code solutions require less coding input and more flexibility, but basic coding knowledge is usually still needed.

Drawbacks of traditional SOAR tools (source)
Workflow orchestration and automation for security teams
- No code or low code - no custom development necessary
- Integrates with all your systems - internal and external
- Built-in safeguards like credential management and change control
A newer approach: no-code automation
Just as SOAR addressed many of the issues faced by SIEMs, no-code workflow automation offers a solution to the challenges facing traditional SOARs. Thanks to their lightweight “drag-and-drop” approach to automating security tasks, no-code automation tools can be used by anyone—not just security engineers with coding knowledge. The people closest to the problem can be actively involved in building the solution.
No-code solutions can be used to automate and orchestrate various security and technology tasks across multiple systems, such as:
Identifying and defining risks
Enforcing security controls
Collecting evidence for compliance activities
Detecting, responding to, and fully remediating incidents and threats
Here is an example of an automated security workflow within a no-code automation tool. This workflow aims to analyze known vulnerabilities from a well-known vulnerability management vendor (in this example, Tenable, although the no-code platform Tines is vendor-agnostic). As you can see, it has multiple triggers to automatically perform discrete tasks, like creating tickets for high risks or posting alerts in a collaboration tool (Slack).
Use a Tines Page to analyze known vulnerabilities from Tenable
Export the latest CSV file from Tenable with known vulnerabilities, and upload the file via a Tines Page to kick off this workflow that creates Jira issues for those high-risk and then notifies a Slack channel.
No-code solutions may also offer additional features, e.g., in-built security features such as:
Single sign-on (SSO)
Support for Security Assertion Markup Language (SAML)
Customized session timeout
Other no-code solutions offer advanced functionality beyond solely automating low-level, manual, repetitive tasks. They can layer security orchestration over automated workflows, enabling faster response via higher-level decision-making by computerized processes. Here’s a high-level example of this in the threat detection domain:
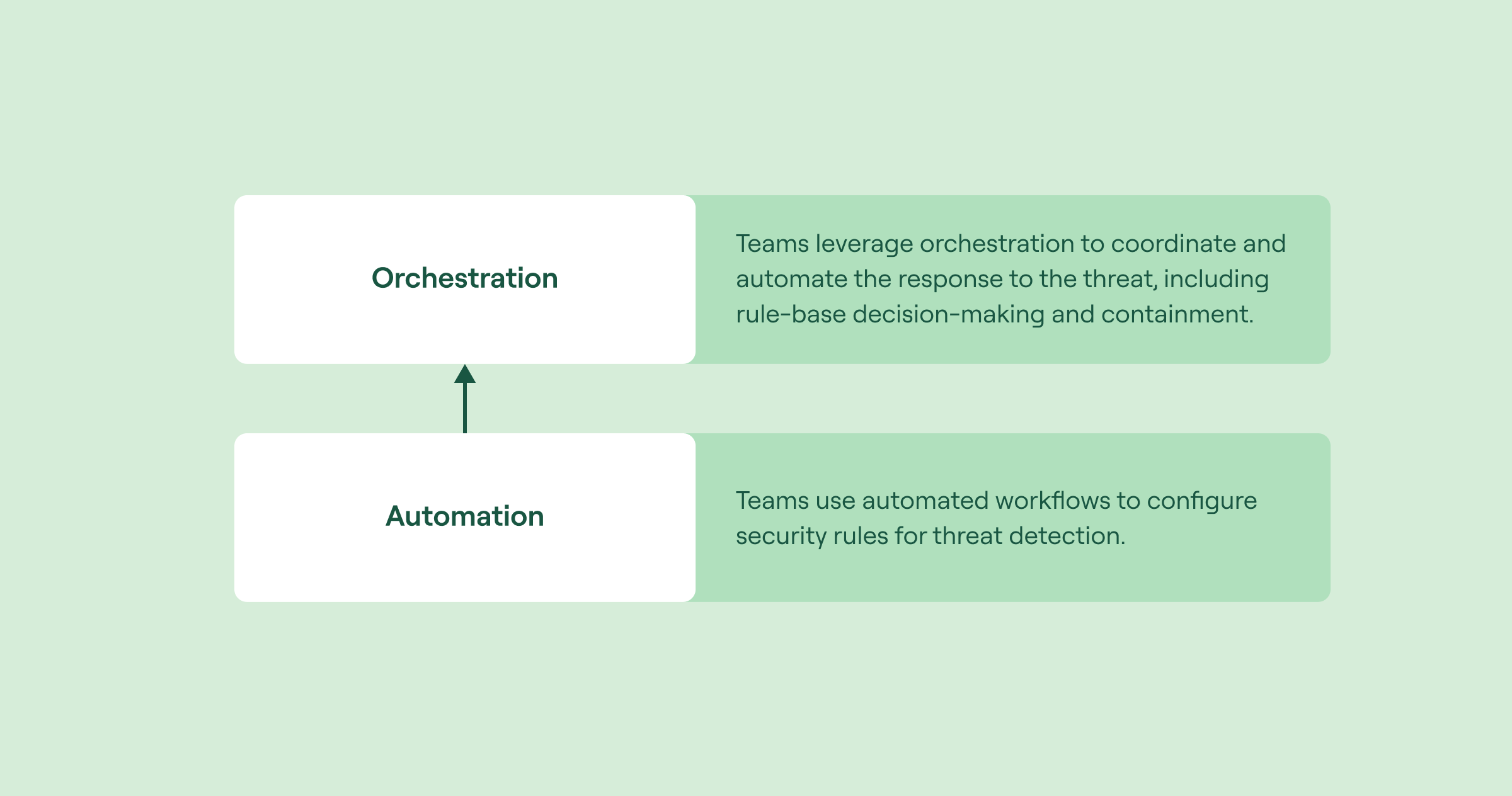
Layering orchestration and automation in threat detection (source)
Here is a practical example showing the difference between automation and orchestration:
Choosing the right no-code solution
As with any tooling purchase, there are various factors to consider. One concern with specific no-code solutions is that some can have limited customization capability, rendering them unable to support more complex business requirements. However, making intentional, informed purchasing decisions can quickly address this concern.
When choosing a workflow automation tool, do all of the following:
Ensure you understand and communicate your company’s requirements (people, process, and technology stack).
Carry out a proof of concept (POC) on one or two test use cases to ensure the solution addresses your needs.
Check that the chosen vendor or solution:
Is easy to integrate with a range of tools and services
Includes in-built security features
Helps you improve your existing processes during POC and beyond
Design a well-defined security workflow automation scope and strategy
Effective security workflow automation requires a clearly defined strategy and scope that meets the needs of the business and any key stakeholders. It’s always best to engage key stakeholders as early as possible in the process.
Estimating the complexity of a manual process
When estimating the effort level or complexity associated with a manual process, various approaches can be used. Two examples are listed below:
The simple, medium, and complex approach, using the number of steps within a process to estimate complexity, for example:
Where processes may require human input
Some processes will still require human insight. When mapping out your processes, ensure that you highlight any places where this is the case. If your process requires a lot of human insight, consider how you can include humans in the automation loop.
Here is a real-world example of where a process may require some level of human input for additional contextual decision-making:
Completing at-source fine-tuning before automating
In addition to identifying any areas of a process that still require human input, organizations should aim to complete any outstanding at-source log-tuning activity before automation deployment. An example of this might be reducing logs of limited value, such as duplicated logs, debug reports, or informational events like routine system notifications. This will help reduce overall log volumes and the number of false positives, thereby maximizing automation value.
Scoping your workflow automation
Once you’ve deduced whether workflow automation is the right choice for your processes, you can begin scoping your workflow automation. Here is a handy scope checklist outlining what to consider when scoping security workflow automation:
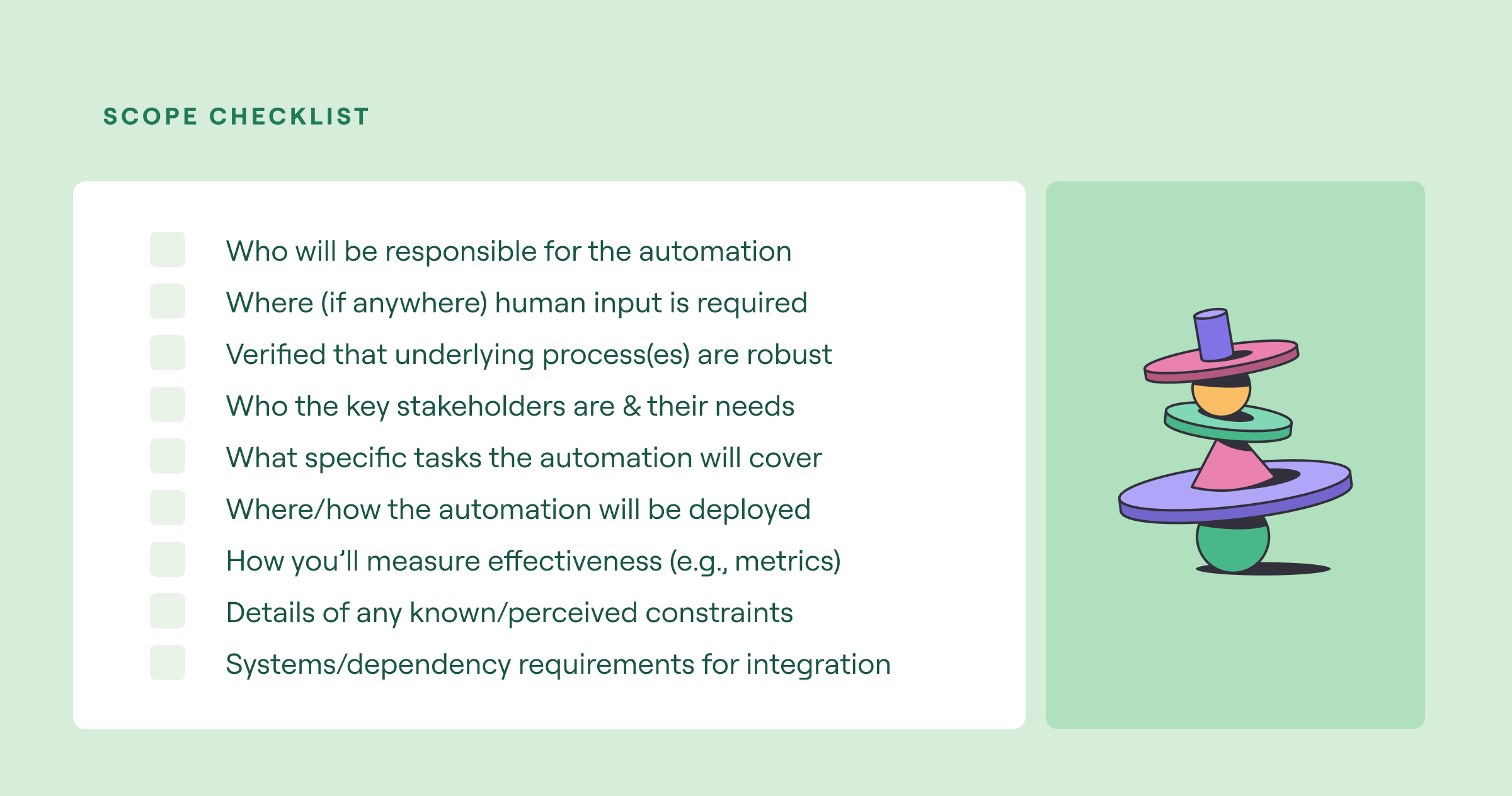
Workflow automation scoping checklist (source)
Measuring effectiveness
You can assess the effectiveness of your automation programs by establishing success criteria and measuring progress with relevant metrics. These success criteria should address the primary objectives of your automation deployment. Choose and prioritize clear, measurable goals (e.g., SMART goals) focused on enhancing security, and regularly review them.
Here are some common success criteria:
Enhancing process efficiency
Bolstering team productivity
Reducing manual errors
Achieving cost savings
Employee satisfaction and retention
Increasing client/customer satisfaction
The table below describes frequently used methods of measurement.
See Tines’ library of pre-built workflows
Ensure that appropriate security tools and processes are in place
Two critical components need to be in place before implementing any workflow automation program: security tools and processes.
Critical workflow components (source)
However, simply having a bunch of security tools and processes is insufficient. You need to verify that you have the right ones to hit the ground running. Let’s address the tools first.
Implementing the right security tools and processes
Each organization's tooling needs will differ depending on its infrastructure, the services it uses or provides, and the unique threats it faces. Effectively leveraging automation requires a security team to have some basic tools in place, such as:
Intrusion detection or monitoring systems (IDS tools or antimalware or antivirus tools)
Firewalls
Collaboration and communication tools, i.e., productivity and real-time messaging tools, like Microsoft Teams and Slack
Remember to check that tools have an API so that workflow automation platforms can connect to them.
More mature security teams may introduce other advanced tools, such as those specialized in:
Threat intelligence and threat hunting
Advanced incident response and/or digital forensics
Malware analysis
Once you’ve sorted your tools, you can focus on your security processes. Remember that automation isn’t a silver bullet for poor processes: Automating a lousy process just means you have an automated process that’s still lousy.
Prioritize well-established processes for automation
When deciding which processes to automate, prioritize well-established ones that solve the problems your organization is most concerned about. For example, perhaps you’re worried about how long it takes human analysts to respond to incidents or threats or the company’s inability to prioritize the remediation of genuine vulnerabilities and threats quickly.
To maximize value, any chosen security processes should:
Have a practical objective focused on addressing key security problems or challenges surrounding resource drain and/or scalability
Be established and working well
Be clear and sequential:
Map out each task step-by-step.
Highlight any activities that run simultaneously as well as any tasks requiring human insight.
Be realistic by comparing against any set budget and against the calculated cost and effort to implement the automation
When you’ve finished mapping a process, test it to ensure it functions as intended. It should align with (and deliver against) its primary objective, cover all necessary tasks, be repeatable, and be well-understood by all relevant stakeholders.
Standardize and iteratively build workflows
Organizations often struggle with where to start, overwhelmed by the possibilities. Many rush to implement automation everywhere they can, but trying to do too much too quickly results in ill-defined and ineffective workflows and wasted time and effort. Security workflows should contain discrete security-related tasks with explicit outcomes. It’s best to begin gradually, breaking processes down into smaller, more manageable steps and building your security automation capability iteratively.
Start by standardizing common security workflows and playbooks. The table below shows some examples of discrete security activities that are often automated.
How to standardize an existing workflow
To see how an existing workflow can be standardized, consider the example of inactive account de-provisioning. This is a common security hygiene workflow that almost every organization needs to implement, but there are multiple ways to do it, each with different dependencies.
To standardize this workflow:
Establish a common identity management and account tracking method.
Define how an inactive account is calculated.
Define what actions to take once an inactive account has been identified.
Define how and where each step is recorded.
The workflow orchestration below demonstrates one way that this could work. First, Okta is established as the identity management system in the example, and it is responsible for tracking when accounts have last been logged in. Second, an inactive account is identified by calculating the days since the last login. Third, once an inactive account has been identified, it is passed to one of three actions: deactivate, suspend, or delete. Fourth, each action is tracked within a case.


Other considerations when standardizing security workflows
Here are some other considerations when standardizing workflows:
Make sure that all tasks are mapped out step by step.
Document all steps.
Be sure that all involved stakeholders fully understand their roles and responsibilities.
Include information about the applicable tools and how they integrate.
Check that all discrete tasks are accessible, consistent, and effective.
Be sure that each task and step is robust and repeatable.
Continuously test and optimize your workflows
Testing your automated workflows before production rollout is vital, but testing shouldn’t be considered a one-time job. We all know technology stacks evolve, as do the needs of a business and its people. Live automated workflows must be regularly tested to ensure efficiency and optimized to improve performance.
These questions will help you test your workflows and identify optimization opportunities:
Does the workflow successfully perform the function it was intended to do?
Is each step essential? Can any steps be condensed now that you’ve established the workflow?
You can optimize workflows through modularization and condensing trigger points down.
You can also look to nest or combine functions to reduce the overall number of actions in a workflow.
Does the workflow return satisfactory results against your defined success criteria and metrics (e.g., reduction in overall MTTR, achieved cost savings, etc.)?
Is the workflow succeeding in making people’s lives easier?
Are there any bottlenecks that are capping efficiency? Can these elements be improved or fine-tuned?
Can a workflow (or a template/test case) be expanded or repurposed across other business areas?
Can you leverage workflows for broader purposes, such as monitoring and orchestrating overall workflow automation?
Did you know Tines' Community Edition is free forever?
- No code or low code - no custom development necessary
- Integrates with all your systems - internal and external
- Built-in safeguards like credential management and change control
Last thoughts
Security workflow automation is a worthwhile addition to any modern security team’s arsenal. These solutions increase efficiency by reducing human effort and optimizing processes, enabling scalability and evolution of operations.
For security workflow automation to be effective, it must:
Have a well-defined scope and clear, practical outcomes aligned to business need
Be the right workflow automation solution (tested via proof of concept) aligned to your unique requirements
Be implemented only after verifying that you have the right security tools and processes in place already
Be standardized, modularized, and built iteratively
Be continuously tested and optimized (leveraging opportunities to condense down, expand, and orchestrate further for added value)